Intellectual Point Announces GI Bill® Approval Intellectual Point, a leading provider of IT training and certification programs, is proud to announce its Virginia State Approving Agency
Expert Insight Blogs

Intellectual Point Announces GI Bill® Approval
Revamped Course Schedule for 2024: Innovations and Returns at Intellectual Point
Revamped Course Schedule for 2024: Innovations and Returns at Intellectual Point By contributor Laurentino Rodrigues At Intellectual Point, we pride ourselves on being at the forefront

Red Ribbon Week – Be Kind to Your Mind, Live Drug FreeTM
Red Ribbon Week – Red Ribbons have been a part of a national campaign since 1985 in response to the murder of special agent Enrique Camarena of

October: Cybersecurity Awareness Month
October: Cybersecurity Awareness Month By contributor Lyan Ware Pumpkin spice everything, cozy sweater weather, spooky movie reruns, and that crisp, lingering bonfire smell in the air
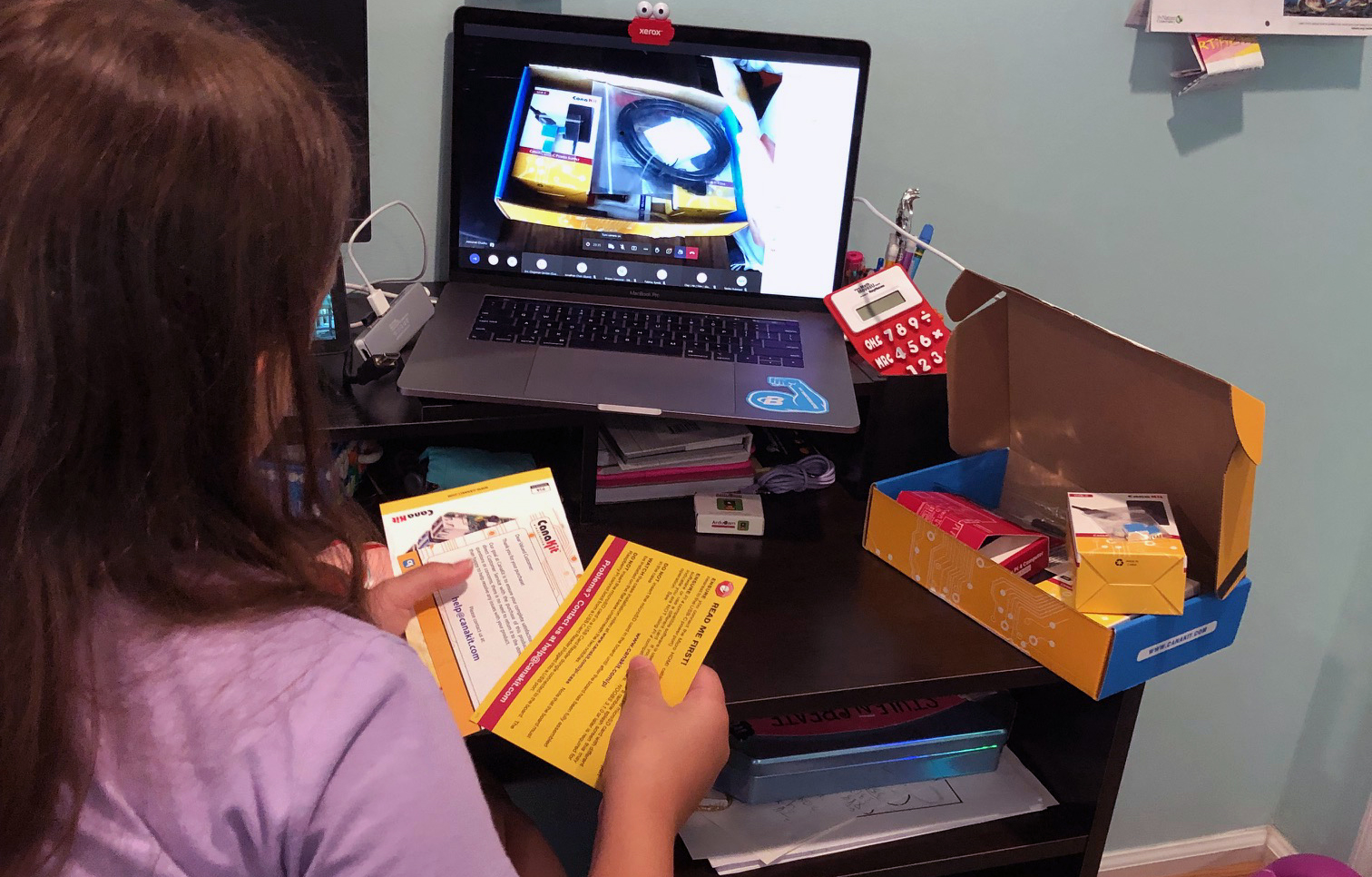
Pre-ETS & Intellectual Point’s STEM Workshops
Pre-ETS & Intellectual Point’s STEM Workshops By contributor Lyan Ware Pre-ETS stands for Pre-Employment Transition Services, a program intended to provide differently abled students with career
The Rise of Prompt Engineers and AI Whispering
The Rise of Prompt Engineers and AI Whispering By contributor Lyan Ware In the era of technological convergence, the symbiotic relationship between human creativity and artificial

The Importance of Secure Coding in Software Development
The Importance of Secure Coding in Software Development By contributor Lyan Ware Secure coding is the practice of developing software that is protected from security liabilities.

Generative AI: A Gateway to Creative Innovation
Generative AI: A Gateway to Creative Innovation by contributor Lyan Ware ChatGPT, DALL-E, and Bard: you’ve either heard of them or used them yourself. These applications

My Career Advancement Account (MyCAA): An Opportunity for Military Spouses
My Career Advancement Account (MyCAA): An Opportunity for Military Spouses By contributor Lyan Ware The transient nature of military life is challenging for military families, especially

The Role of Penetration Testing in Strengthening Cybersecurity
The Role of Penetration Testing in Strengthening Cybersecurity By contributor Lyan Ware Penetration testing, also known as ethical hacking or white hat attack, is a crucial
The Future is Now: Consider a Career in Robotics
The Future is Now: Consider a Career in Robotics By contributor Lyan Ware With algorithms and automations taking increasing responsibility for making our world go
Key Differences Between White Hat, Black Hat, and Grey Hat Hackers
Key Differences Between White Hat, Black Hat, and Grey Hat Hackers By contributor Lyan Ware As far as hackers go, they come in various shades,

The Growing Field of Cybersecurity: Career Opportunities and Skills Needed
The Growing Field of Cybersecurity: Career Opportunities and Skills Needed By contributor Lyan Ware Whether you’re a budding cyber enthusiast or an experienced IT professional looking

Cybersecurity Best Practices for Small Businesses
Cybersecurity Best Practices for Small Businesses By contributor Lyan Ware Cybersecurity is not just a concern for large corporations; small businesses are also vulnerable to cyberattacks.

Exploring the World of Ethical Hacking and Certified Ethical Hacker (CEH) Certification
Exploring the World of Ethical Hacking and Certified Ethical Hacker (CEH) Certification by contributor Lyan Ware With cyber threats escalating in complexity and frequency, ethical hacking

Benefits of The CompTIA Security+ Certification
Benefits of The CompTIA Security+ Certification By contributor Lyan Ware Our continued reliance on social media and digital interconnectivity means that individuals and organizations must prioritize
Understanding the Role of Cybersecurity Analysts
Understanding the Role of Cybersecurity Analysts By contributor Lyan Ware For decades, the media has portrayed digital defenders as lonely hackers: hoodie-wearing, sleepy-eyed anti-heroes and nerdy

Introduction to Certified Information Systems Security Professional (CISSP) Certification
Introduction to Certified Information Systems Security Professional (CISSP) Certification By contributor Lyan Ware Welcome, fellow cybersecurity enthusiasts! In this blog, we’re going to delve into the

Common Cybersecurity Threats and How to Protect Yourself
Common Cybersecurity Threats and How to Protect Yourself By contributor Lyan Ware Welcome to the digital age, where our lives intertwine with technology more than ever

Importance of Cybersecurity in Today’s Digital World
Importance of Cybersecurity in Today’s Digital World By contributor Lyan Ware When shopping for appliances, it appears that no function is too mundane to be enhanced

Why You Need CompTIA’s Security+ For Your Federal Career
Why You Need CompTIA’s Security+ For Your Federal Career By contributor Lyan Ware Continuous advancements in tech produce waves of even more sophisticated threat actors who

How to Setup Your Ethical Hacking Home Lab
How to Setup Your Ethical Hacking Home Lab By contributor Lyan Ware Creating a virtual home lab for ethical hacking is a great way to develop

The Importance of Human Centered Security Design
The Importance of Human Centered Security Design By contributor Lyan Ware In my previous blog post Is Cyberpunk Becoming Reality? I discuss how the implication
Learn About Vectra AI to Boost Your Cybersecurity Career
Learn About Vectra AI to Boost Your Cybersecurity Career By contributor Lyan Ware What is Vectra AI? Vectra AI provides AI-driven threat detection and response for

Network Your Way into Your Dream Cybersecurity Job
Network Your Way into Your Dream Cybersecurity Job By contributor Lyan Ware Even after working hard to obtain your IT certifications and tinkering painstakingly to

Unique Cybersecurity/IT Jobs
Unique Cybersecurity/IT Jobs By contributor Lyan Ware When thinking about job roles in cybersecurity, we typically conjure images of UV-deprived hermits lit only by a cold glow

Resume Hack for Inexperienced Cybersecurity Professionals
Resume Hack for Inexperienced Cybersecurity Professionals By contributor Lyan Ware For those trying to break into the cybersecurity job market, it can be very difficult when

Intellectual Point Continues Its Platinum Status as a CompTIA Partner
Intellectual Point Continues Its Platinum Status as a CompTIA Partner As a leading provider of IT and business training, Intellectual Point proudly continues its commitment to

A Successful Future With Early STEM Exposure
A Successful Future With Early STEM Exposure By contributor Lyan Ware With our rapidly evolving world becoming increasingly reliant on automation, it’s important to start thinking about

10 Signs a Job Post is a Scam
10 Signs a Job Post is a Scam By contributors Tyler Daniels & Lyan Ware You didn’t apply to the job You might get contacted by
Do I Need to Learn Coding to Get into Cybersecurity?
Do I Need to Learn Coding to Get into Cybersecurity? By contributor Lyan Ware Many people interested in a career transition into cybersecurity are hesitant to
What Skills Transfer into IT and Cybersecurity?
What Skills Transfer into IT and Cybersecurity? By contributor Lyan Ware Thinking about breaking into the cyber security and information technology industry, but don’t have much

Which Certs Are Right for Me?
Which Certs Are Right for Me? By contributor Lyan Ware Thinking of a career transition into IT, but don’t know where to start? Here’s a

10 Things to Avoid When Talking to a Recruiter
10 Things to Avoid When Talking to a Recruiter Contributors: Tyler Daniels and Lyan Ware Asking easily researchable questions: Not doing any preliminary research is a sure

Tips on Becoming a Better Interviewee
Tips on Becoming a Better Interviewee By Lyan Ware contributor Despite being an amazing candidate on paper, a person can easily blow an interview by not being
Top 5 Tips for Taking an Exam at Intellectual Point
Top 5 Tips for Taking an Exam at Intellectual Point Did you know that Intellectual Point has a full-service testing center at their physical site in Sterling,

Is Cyberpunk Becoming Reality?
Is Cyberpunk Becoming Reality? By Lyan Ware Contributor The Matrix, Terminator, and Bladerunner film franchises are all futuristic dystopian movies categorized under the science fiction subgenre

Top Tips on Interaction with Recruiters on LinkedIn
Top Tips on Interaction with Recruiters on LinkedIn By Lyan Ware Contributor Networking plays a significant role in landing a job interview when you’re actively

What UiPath Course is Best for You?
What UiPath Course is Best for You? Are you ready to Automate your Career with UiPath? There are several different options for classes and certifications depending on

Interview with Intellectual Point Alumni Jackson Dollar
Interview with Intellectual Point Alumni Jackson Dollar By Lyan Ware Contributor Many students come to Intellectual Point with little-to-no experience in IT and cybersecurity. They are

Apex Systems, Partnering with Veterans for Career Success
Whether you’re in the field or just starting to consider a career in IT, you can move forward knowing that the opportunities are there for you and

Tips on Using LinkedIn for Job Searching
Tips on Using LinkedIn for Job Searching By Lyan Ware Contributor Having an optimized LinkedIn profile is a must-have for professionals and job seekers. In order

American Airlines Becomes Victim of a Phishing Attack
By Lyan Ware Contributor In a letter sent to the office of the New Hampshire Attorney General, a lawyer representing American Airlines detailed a security breach

How to Gain Cyber Security Experience for Your Resume
How to Gain Cyber Security Experience for Your Resume By Lyan Ware Contributor Once you’ve got your certifications, how do you compete in the cyber security
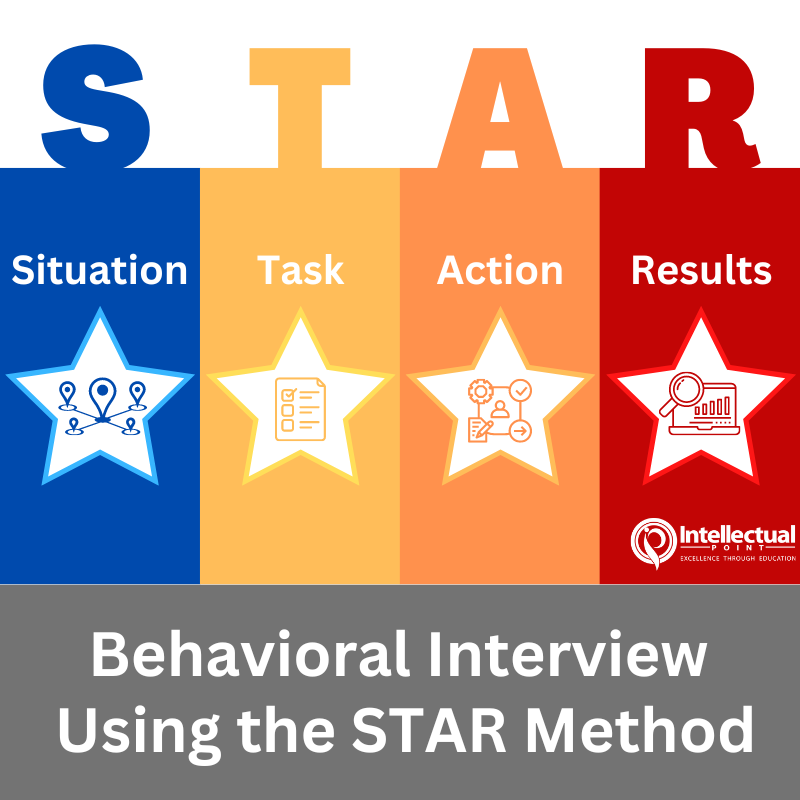
Behavioral Interview Using the STAR Method
Behavioral Interview Using the STAR Method Situation: Describe the situation that you were in or the task that you needed to accomplish. You must describe a specific event

Ways to Break into the Cyber Security Industry
Ways to Break into the Cyber Security Industry By Lyan Ware Contributor Let’s say, you’ve nailed your exams and got the certifications: check. You’ve created an
Time to Automate (RPA) Your Career!
Are you Ready to Stay on Top of an Evolving Change in the Industry? Robotic Process Automation provides businesses a simple method to consolidate mundane
It is Time to Share your EC Council Certification Badge!
EC Council Certification Badges and How to Share Them A Digital Badge is a way for you to share your EC Council/Aspen achievements. It’s a badge that

Interviewing Tips for Success
Interviewing Tips for Success By Lyan Ware Contributor So, you’ve managed to compile a polished resume that made it pass the AI filtering systems, human resources,

How To Get A Job in Help Desk
How To Get A Job in Help Desk By Lyan Ware Contributor Help Desk aka IT Support is an entry-level position in the IT/Cyber-related field. Help
How to get a Job as a SOC Analyst
How to get a Job as a SOC Analyst By Lyan Ware Contributor Cyber-security analysts or SOC analysts are part of the team that protects organizations

5 Reasons why you should use LinkedIn
5 Reasons why you should use LinkedIn By Lyan Ware Contributor With over 500 million members worldwide, LinkedIn is the most popular social media platform made

What it’s like being a Cyber Forensics Investigator
What it’s like being a Cyber Forensics Investigator By Lyan Ware Contributor The role of a cyber forensics investigator usually entails providing evidence for legal cases

What is it like being a CISO?
What is it like being a CISO? By Lyan Ware Contributor A CISO, or chief information security officer holds considerably one of the highest paying salaries
How to Pass your CompTIA A+ Exam
How to Pass your CompTIA A+ Exam If you’re looking to get A+ certified, a great tool to utilize is the CompTIA website (www.comptia.org). Not only does

What it’s like being a Penetration Tester/Ethical Hacker
What it’s like being a Penetration Tester/Ethical Hacker By Lyan Ware Contributor Penetration testers or ethical hackers conduct different types of cyber security assessments for their

Ways To Combat Burnout
Ways To Combat Burnout By Lyan Ware Contributor We all experience stress, frustration, and fatigue at different time points in life (several, in fact), but when

What it’s like being a SOC Analyst
What it’s like being a SOC Analyst By Lyan Ware Contributor Security Operations Analysts, or SOC Analysts are regarded as the front line for triaging progressing

Tech is Taking Over. Are You Ready?
Tech is Taking Over. Are You Ready? In 2022, the U.S. has the largest tech market of any country making up 33% of the total market worldwide,

Ways to Deal with Test-Taking Anxiety
Are you getting ready for your exam? Here are some helpful tips to make sure you are ready! Ways to Deal with Test-Taking Anxiety: Develop healthy habits:

A Day in the Life of a Cloud Security Engineer
What it’s like being a Cloud Security Engineer By Lyan Ware Contributor A client or project manager will give you a list of requirements or rules

Tips On Improving Your Resume
Tips On Improving Your Resume Ever heard of the old acronym “K.I.S.S”? It stands for “Keep It Simple, Stupid” and it applies to resumes, believe it

Why Veterans Should Consider a Cybersecurity Career
Why Veterans Should Consider a Cybersecurity Career By Lyan Ware Contributor Civilian life can be intimidating to navigate after leaving the military, especially when it comes

It is Time to Share Your CompTIA Certification Badges!
CompTIA Certification Badges – How to Share Them A Digital Badge is a way for you to share your CompTIA achievements. It’s a badge that contains specific

Cyber Security Job Market is Booming
Cyber Security Job Market is Booming The demand for jobs in the cyber security field have increased by 43% in the last year, with employers in the
ZuoRAT: Multi-stage Malware hits the Streets
ZuoRAT: Multi-stage Malware hits the Streets A multistage remote access trojan that has been active since April is targeting SOHO routers from CISCO Systems, Netgear, ASUS and
Follina: An Update – Patched and fixed
Follina: An Update – Patched and fixed The new Microsoft Word exploit discovered earlier this year that could secretly run malware on your computer was patched in

Five steps to becoming a Successful Hacker
Five steps to becoming a Successful Hacker 1) Learn the computer basics. You need a sufficient level of knowledge on computer networks. This isn’t required,

Bug Bounty Hunting – Can this be your full-time job?
Bug Bounty Hunting – Can this be your full-time job? Bug hunting is a trendy side gig, and several reports have been published showing that many ethical

5 Security Habits to Start Right Now
5 Security Habits to Start Right Now Password Hygiene – That’s right. You guessed it. If you haven’t changed that password in a while, you probably
Summer STEM Camp for Kids 13 Years and older at Intellectual Point!
Summer STEM Camp for Kids 13 Years and older at Intellectual Point! This summer is going to be awesome at Intellectual Point! We have 5 brand new

Ishan Jadhwani – Tech Wunderkid – Featured in Loudoun NOW
Ishan Jadhwani – Tech Wunderkid – Featured in Loudoun NOW Ishan Jadhwani is the senior Director of Technology Services at Intellectual Point. Ishan is only 16
Come Join Our UiPath RPA Associate Developer Masterclass!
Come Join Our UiPath RPA Associate Developer Masterclass! Intellectual Point is proud to announce our new On Demand UiPath RPA Associate Developer Masterclass! Learn how to automate

Don’t Miss These Upcoming Veteran Events
Don’t Miss These Upcoming Veteran Events We are always looking for ways to support our Veterans. We have found some great events that you should attend.

Are you ready to become a UiPath Certified Professional?
Are you ready to become a UiPath Certified Professional? UiPath Certified Professional is a high-stakes certification program designed to help you advance your career in robotic process

Check Out The NVIDIA GTC GPU Technology Conference Recap
Check Out The NVIDIA GTC GPU Technology Conference Recap Did you catch the March 2022 NVIDIA GTC AI conference? This global experience brought together thousands of innovators

Intellectual Point Sponsored a Loudoun County High School Cybersecurity Event
Intellectual Point Sponsored a Loudoun County High School Cybersecurity Event Loudoun County Public High School hosted a new event called “Cyberslam” on Saturday, April 2, 2022. Intellectual

You can now use Affirm’s flexible payment for Intellectual Point Classes!
You can now use Affirm’s flexible payment for Intellectual Point Classes! Affirm is a new payment method allowing for different payment options. You can shop and pay
How to Pass the CompTIA Security+ Exam at the First Attempt
How to pass the CompTIA Security+ Exam at the First Attempt First, you need to familiarize yourself with what is on the test. Get to know
Check Out These Two New ISACA Certification Classes at Intellectual Point!
Check Out These Two New ISACA Certification Classes at Intellectual Point! Are you a technical professional who wants to help organizations mitigate risks and optimize ROI in

Follow These 7 Tips to Start Your IT Career!
Follow These 7 Tips to Start Your IT Career! Are you interested in starting a career in IT or Cyber Security? It does not matter what your

Closing the Data Skills Gap with CompTIA Data+
Closing the Data Skills Gap with CompTIA Data+ CompTIA Data+ is an early-career data analytics certification for professionals tasked with developing and promoting data-driven business decision-making.

Press Release – Intellectual Point’s Certification Courses Approved for GI Bill® Reimbursement
Intellectual Point’s Certification Courses Approved for GI Bill® Reimbursement by the Virginia State Approving Agency (Sterling, VA) – On February 14, 2022, Intellectual Point received official notice

Introducing Certified Cloud Security Engineer (C|CSE)
Introducing Certified Cloud Security Engineer (C|CSE) EC-Council’s Certified Cloud Security Engineer (C|CSE) course is curated by cloud security professionals in association with renowned subject matter experts to
What is Robotic Process Automation (RPA) & Intelligent Automation?
What is Robotic Process Automation (RPA) & Intelligent Automation? Robotic process automation (RPA) is a software technology that makes it easy to build, deploy, and manage software

Are you Ready to Step into the Metaverse?
Are you ready to step into the Metaverse? The metaverse has been a hot topic of conversation with Facebook (Meta) and Microsoft both already stepping into

Great Veteran Events For 2022
Virtual Veteran Job Fair 2022 Are you a Veteran looking for a job in Information Technology (IT)? Join us for this unique event where you could walk away

Top RPA Careers and What Certs you Need!
Top RPA Careers and What Certs You Need! Robotic Process Automation (RPA) jobs are in high demand. The need for RPA-trained and skilled individuals is global.
STEM Cyberwarriors Camp 2022
STEM Cyberwarriors Camp 2022 JOIN US FOR INTELLECTUAL POINT’S CYBERWARRIORS CODING & AUTOMATION EXPERTS VIRTUAL HANDS-ON CAREER EXPLORATION STEM WORKSHOPS! These will be hands-on career exploration
Important Apache Log4j2 Security Vulnerability
Important Apache Log4j2 Security Vulnerability The open-source Apache library Log4j is subject to a significant security vulnerability, which became widely publicized and actively exploited beginning Friday, December

Are you ready to prove your expertise with robotic process automation (RPA)?
Are you ready to prove your expertise with robotic process automation (RPA)? Robotic Process Automation does not mean the “Terminator” is going to take over. Rest assured

Top 5 Cyber Security Certifications for Entry-level Roles In 2022
Top 5 Cyber Security Certifications for Entry-level Roles In 2022 There are many compelling reasons to pursue a career in cyber security. One of the top reasons

Are you ready to climb to the top of the enterprise security ladder?
Are you ready to climb to the top of the enterprise security ladder? Your cyber security career has many different paths you can take. Have you thought
What is your Cyber Security Career Path?
What is your Cyber Security Career Path? At Intellectual Point, we are here to help you find the best career path for your future. There are many

Are you ready for the CompTIA PenTest+ PT0-002 Exam?
Are you ready for the CompTIA PenTest+ PT0-002 Exam? The CompTIA PenTest+ certification is a vendor-neutral, internationally targeted validation of intermediate-level penetration testing (or pen testing) knowledge and
Are you ready for the CASP+ CAS-004 Exam?
Are you ready for the CASP+ CAS-004 Exam? The CompTIA Advanced Security Practitioner (CASP+) certification is a vendor-neutral credential and internationally targeted validation of advanced-level cybersecurity skills and
CompTIA Network+ Exam Updates for N10-008
CompTIA Network+ Exam Updates for N10-008 Organizations and IT professionals face new network challenges and complexities as they navigate through increased security concerns, hybrid working environments, and the need

How Veterans Can Get the Same ‘Reskilling’ Training Open to Civilians
How Veterans Can Get the Same ‘Reskilling’ Training Open to Civilians Have you had a chance to read the “How Veterans Can Get the Same ‘Reskilling’

Why Should You Get Your CRISC?
Get your CRISC with Intellectual Point Today! ISACA’s Certified in Risk and Information Systems Control (CRISC) certification is ideal for mid-career IT/IS audit, risk, and security professionals.
How to use VirtualBox 101
How to use VirtualBox 101 VirtualBox is designed to run virtual machines on your physical machine without reinstalling your OS that is running on a physical machine.
Press Release On-Demand Federal Sales Certification Training Course
For Immediate Release: August 11, 2021 Intellectual Point is Launching a New On-Demand Federal Sales Certification Training Course on its Rapid Education Platform Sterling VA, August

Calling all Veterans, we have some great career opportunities for you!
Calling all Veterans, we have some great career opportunities for you! Intellectual Point is dedicated to our student veterans. We are here to support your needs

Intellectual Point Awarded Prime Contract on Department of Defense Navy SeaPort Next Generation (NxG)
For Immediate Release: July 30, 2021 Intellectual Point Awarded Prime Contract on Department of Defense Navy SeaPort Next Generation (NxG) Sterling VA, July 30, 2021 –

How to Take your Cybersecurity Career to the Next Level!
How to Take your Cybersecurity Career to the Next Level! If you already have cybersecurity experience the odds are you are ready to take your career to

Trojans and RATs – CompTIA Security+ SY0-601
Trojans and RATs – CompTIA Security+ SY0-601 Remote access trojans (RATs) give the attacker access to a variety of information on the infected device, including text messages,

Is CISSP the next Certification for you?
Is CISSP the next Certification for you? The Certified Information Systems Security Professional (CISSP) is one of the world’s most valued information technology and information security certifications.

Most In-Demand Cybersecurity Skills to have Today!
Most In-Demand Cybersecurity Skills to have Today! As you already know there is a big shortage of skilled candidates to fill thousands of open cybersecurity jobs. There

CompTIA’s New Data Analytics Certification
CompTIA’s New Data Analytics Certification Data is everything when you are making important business decisions. Data analytics is one of the top skills IT pros should have
Day 1 of STEM Summer Camp at Intellectual Point is in the Books!
Day 1 of STEM Summer Camp at Intellectual Point is in the Books! The first day of summer camp started today at Intellectual Point. We had a

Top Tips for Using Your LinkedIn Profile
Top Tips for Using Your LinkedIn Profile Be Mindful of Your Profile Settings If you’re job searching, you can adjust your profile settings to let recruiters

Top Tips to Set Up a Successful LinkedIn Profile in the Individual Sections
Get a Custom URL When you create a profile, LinkedIn automatically assigns you a string of numbers as a URL. But you can (and should) set a

Top LinkedIn Tips to Optimize Your Profile
Top LinkedIn Tips to Optimize Your Profile Use Your LinkedIn to Tell a Story and Build Your Personal Brand When you are building your LinkedIn profile,

Ransomware Attacks In Our Digital World
Ransomware Attacks In Our Digital World The rise of ransomware attacks is on the rise and is not slowing down. Over the last month, the U.S. has
LinkedIn Learning is Now Available at NO COST to Northern Virginia WIOA Jobseekers!
LinkedIn Learning is Now Available at NO COST to Northern Virginia WIOA Jobseekers! Virginia Career Works has a new initiative to help students with free training. The

What is Cybersecurity Mesh?
What is Cybersecurity Mesh? You can create a Cybersecurity Mesh by designing and implementing an IT security infrastructure that is not focused on building a single ‘perimeter’
Biden signed an executive order to strengthen the United States’ cyber defense practices
Biden signed an executive order to strengthen the United States’ cyber defense practices Ransomware attacks are on the rise and we are feeling the strong impact of
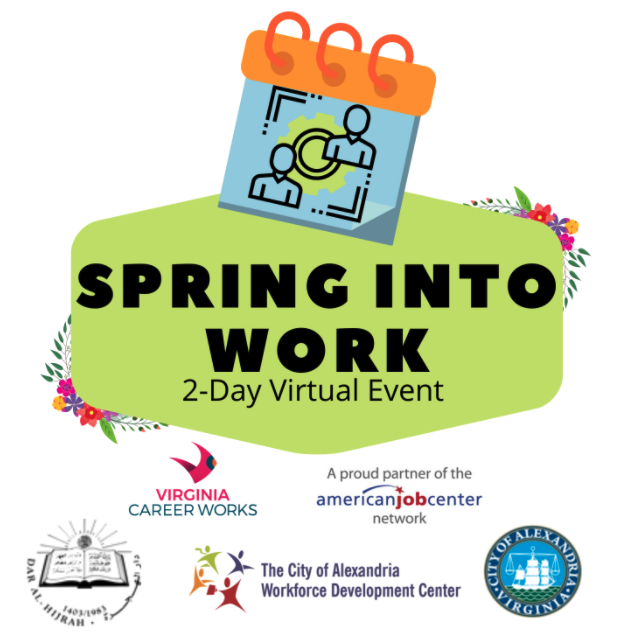
Spring Into Work – A 2 Day Virtual Event
The 2nd Annual Spring Forward Virtual Job Fair Virginia Career Works – Capital Region would like to invite you to the 2nd Spring Forward Virtual Hiring Event.

Pen Testers Discover a Security Bug on Peloton’s Servers
Pen Testers Discover a Security Bug on Peloton’s Servers Once COVID hit people were all jumping on the Peloton bike to stay fit in the safety of

Help Has My Phone Been Hacked?!?!
Help Has My Phone Been Hacked?!?! Smartphones are the main hub of our online lives from email to banking. They never leave your side and are a

Your Cyber Security Career Plan is a Business Plan!
You are the Product, the Service, and the Provider with your own Brand and Competitive Edge in the Cyber Security Marketplace As a Career Services Specialist, Career

Reasons to Pursue a Career in Cyber Security
Reasons to Pursue a Career in Cyber Security What do we look for when considering a new career? As a Certified Professional Resume Writer and Career Coach,

What you need to know about the new CompTIA Cloud+ (CV0-003)
What you need to know about the new CompTIA Cloud+ (CV1-003) CompTIA Cloud+ is a global certification that validates the skills needed to deploy and automate secure

How to Launch Your Cloud Career Without Experience!
How to Launch Your Cloud Career Without Experience! There is never a better time to start than now! You can’t run a business without cloud computing especially

On July 31, 2021, CompTIA will be retiring the CompTIA Security+ (SY0-501) exam
On July 31, 2021, CompTIA will be retiring from the CompTIA Security+ (SY0-501) exam CompTIA Security+ (SY0-501) English language exam will retire on July 31, 2021. The

Is your Resume ATS-Optimized and Going to Land you an Interview?
During our Digital Natives Meetup Group on April 6th, we discussed effective methodologies and an ATS-optimized approach to writing resumes that will land you the new job

What is Internet of Behaviors (IoB)?
What is the Internet of Behaviors (IoB)? The Internet of Behavior extends from the Internet of Things (IoT), the interconnection of devices that results in a vast

Come Join Our Team! Director, Veteran Student Center
Director, Veteran Student Center POSITION IDENTIFICATION TITLE Director, Veteran Student Center GENERAL FUNCTION The Director, Veteran Student Center is responsible for the overall management and operation of the

Did you get your COVID Vaccine yet?
Did you get your COVID Vaccine yet? As we turn the corner into the next phase of the COVID pandemic, the landscape continues to change. Some States

Military, Veterans, and Family and/or cleared candidates In-Person & Virtual Job Fairs!
If you are Military, Veterans, and Family and/or cleared candidates here are some great Job Fair Opportunities! Patuxent River, MD TUESDAY, APRIL 20, 2021 (IN-PERSON &

Calling all CyberWarriors, Join us for Summer Camp 2021!
Calling all CyberWarriors, Join us for Summer Camp 2021! Summer Camp Registration for 2021 is Live! We are excited to announce the CyberWarriors Coding & Automation Experts

Happy International Women’s Day 2021!
Happy International Women’s Day 2021! That past year has been fraught with challenges and unprecedented change. But the silver lining has been the focus on ensuring everyone

Prem Jadhwani will be speaking at the ISSA August 17th Chapter meeting!
Join us on Tuesday, August 17 for the ISSA monthly National Capital Chapter meeting with a special guest speaker Prem Jadhwani! Creating the Next Generation of
Are you ready to Protect, Detect, and Respond to threats on a network?
Are you ready to Protect, Detect, and Respond to threats on a network? Achieve your Certified Network Defender (CND) and join the blue team. The CND is
The Future of Business Process Automation
If you’ve imagined yourself managing sophisticated IT processes, becoming an invaluable resource to your organization, and being part of the revolution of how businesses do business,

Why Get Amazon Web Services (AWS) Certified Solutions Architect – Associate Certified?
Why Get Amazon Web Services (AWS) Certified Solutions Architect – Associate Certified? Amazon has infiltrated almost every aspect of consumerism, but what many people don’t know is

What is a Cybersecurity Hiring Manager Looking for?
What is a Cybersecurity Hiring Manager Looking for? Everyone knows that looking for a job is a full-time job! With a competitive job market and many people

Advance your Career with a Federal Sales Certificate with Intellectual Point!
Advance your Career with a Federal Sales Certificate with Intellectual Point! Business as usual – isn’t. Things have changed in both small and significant ways. And as

Quick Ways to Ratchet up Your Resume
Quick Ways to Ratchet up Your Resume It is imperative, now more than ever, to truly differentiate yourself from a prospective employer. Your experience, your expertise, and

Are you ready to make $15,000 more with skills you already have?
Are you ready to make $15,000 more with skills you already have? The New Federal Reserve tool shows how workers can earn $15,000 more with skills they

Which one, Penetration Testing or Certified Ethical Hacking?
CompTIA PenTest+ or Certified Ethical Hacking, which one is right for me? Pen testers, much like Ethical Hackers, often employ the same concepts and tactics in order

VMware Certification Tracks at Intellectual Point!
VMware Certification Tracks at Intellectual Point! We are proud to offer VMware Certifications at Intellectual Point. These certifications validate the critical skills required to integrate and manage

How to Identify and Mitigate the Impact of the Sunburst Hack
How to Identify and Mitigate the Impact of the Sunburst Hack Sunburst Attack Overview On December 13th, 2020 the world became publicly aware of a sophisticated and

How to Get Into Cybersecurity With No Experience?
How to Get Into Cybersecurity With No Experience? Look at your current background and job role Are you made for a cybersecurity position? Most people who go

Why Get Certified Ethical Hacker (CEH) Version 11 Certified?
Why Get Certified Ethical Hacker (CEH) Version 11 Certified? A Certified Ethical Hacker is a specialist typically working in a red team environment, focused on attacking computer

How to Work Cyber Security into your Day-to-Day Life
How to Work Cyber Security into your Day-to-Day Life With high-profile data breaches, advertisers tracking every bit of content you consume, and unwelcomed individuals prying through your

Check out the New RPA Training – UiPath Citizen Developer Foundation
Check out the New RPA Training – UiPath Citizen Developer Foundation UiPath RPA Citizen Developer Foundation is a new solution to change the way work is done

Top Reasons to Get CompTIA PenTest+ Certified
Why Should I Get CompTIA PenTest+ Certified? CompTIA PenTest+ is the industry standard for validating that cybersecurity professionals can perform tasks on systems through penetration testing and

How to Start Your RPA Career!
How to Start Your RPA Career Robotic process automation (RPA) can help your business be more efficient, agile, and profitable. It can make customers’ experiences richer by

Don’t Miss The Fairfax County Cyber/Cloud Virtual Career Fair!
Cyber/Cloud Virtual Career Fair We know how hard you have worked to achieve your certifications with us. It is time to put your success to the test!
Why Should I Get CompTIA ITF+ Certified?
Why Should I Get CompTIA ITF+ Certified? CompTIA IT Fundamentals (ITF+) is the industry standard for an introduction to basic IT knowledge and skills. CompTIA ITF+ establishes

Remote Work will be the Biggest Jobs Trend Carrying into 2021
How COVID Affected Work-From-Home Policies The pandemic devastated industries worldwide this past year but many of the surviving businesses have been able to continue operations through remote work and limited time

Cybersecurity Trends for 2021
2021 is FINALLY here and so are these Cybersecurity Trends! 2020 was a uniquely challenging year in many, many ways but it presented us with some exciting

Boost your career, transform society with UiPath Certifications!
Intellectual Point is offering UiPath Certification Classes Are you ready to take your Robotic Process Automation to the next level? Did you know UiPath has certifications? The

Calling all Software Developers and Network Professionals!
Calling all Software Developers and Network Professionals! It is time to get your Cisco DevNet Certification. Getting Cisco DevNet certification will allow you to prove your skills

How to land a Penetration Testing Job
How to land a Penetration Testing Job Penetration testing — also called pen testing or ethical hacking — is the practice of testing a computer system, network,

Governor Northam Announces Administration Appointments
FOR IMMEDIATE RELEASE: December 22, 2020 Governor Northam Announces Administration Appointments (Sterling, VA) – Governor Ralph Northam of Virginia has announced additional appointments to his Administration.

How to Create a Professional LinkedIn Profile for IT Jobs
How to Create a Professional LinkedIn Profile for IT Jobs At our last Digital Natives Meetup, Prem Jadwani talked about how to create the best LinkedIn profile.

CISA is seeking high school, undergraduate and graduate PAID internships
HOT! Help Spread the Word – The application Deadline is Jan 6, 2021. CISA is seeking high school, undergraduate and graduate PAID internships. Cybersecurity & Infrastructure Security

Why Should I take Certified Ethical Hacker (C|EH) at Intellectual Point?
Why Should I take Certified Ethical Hacker (C|EH) at Intellectual Point? Penetration testing and the certifications that go along with it are hot topics of conversation in

Is your Resume Ready for 2021?
Is your Resume Ready for 2021? Is your resume ready for 2021? We are ready for what the new year has to offer. This is the perfect

Announcing a New Leadership Training at Intellectual Point!
Leadership…It Takes a Team Join us for a free Virtual seminar with executive coach John Gronski. John will walk you through an exciting journey of self-awareness and leadership

CompTIA PenTest+ Is Approved for DoD 8140/8570.01-M
CompTIA PenTest+ Is Approved for DoD 8140/8570.01-M PenTest+ is compliant with ISO 17024 standards and approved by the US DoD to meet directive 8140/8570.01-M requirements. Regulators and

FOR IMMEDIATE RELEASE
FOR IMMEDIATE RELEASE Intellectual Point has been approved as a Private Provider for Virginia’s Registered Apprenticeship (Sterling, VA) – Intellectual Point has announced that it

Why you need to get ITIL® Certified Today!
Why you need to get ITIL® 4 Certified Today! Information Technology Infrastructure Library (ITIL®) is considered the cornerstone and industry-standard best practice framework for supporting, managing, and

Have you heard about the Workforce Innovation and Opportunity Act (WIOA) Program?
Have you heard about the Workforce Innovation and Opportunity Act (WIOA) Program? The Workforce Innovation and Opportunity Act (WIOA) offers an integrated and comprehensive range of services
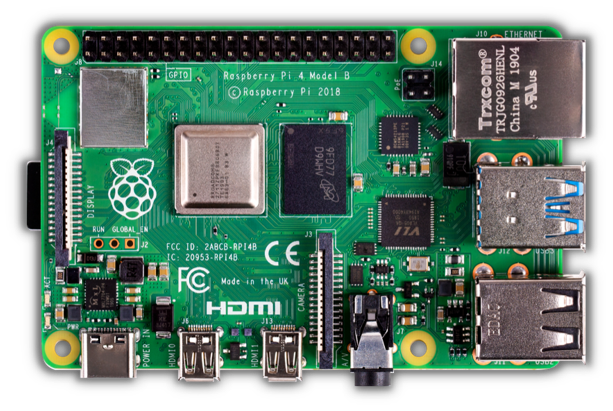
Watch out the Raspberry Pi is not as basic as you think!
Watch out the Raspberry Pi is not as basic as you think! The Raspberry Pi is a low cost, credit-card sized computer that plugs into a computer monitor

Hurry and Apply for the Re-Employing Virginians (REV) Initiative!
Hurry and Apply for the Re-Employing Virginians (REV) Initiative! The Re-Employing Virginians (REV) Initiative offers those whose employment has been impacted by COVID-19, the opportunity to upgrade their skills through
Are Certifications just as valuable as College Degrees?
Are Certifications just as valuable as College Degrees? It used to be that that college was a sure-fire way to get your foot in the door at

One-on-One Career Advice Sessions
One-on-One Career Advice Sessions Act fast because these sessions will fill up quickly! We are introducing a new way for you to seek career advice at Intellectual

Why you need to get Cisco CCNA Certified!
Why you need to get Cisco CCNA Certified! Want to get CCNA certified? Well! The CCNA (Cisco Certified Network Associate) will serve as a foundation pillar in

Friendly Reminder about the PMP Exam Change On 2 January 2021!
Friendly Reminder about the PMP Exam Change On 2 January 2021! The Project Management Institute (PMI)® announced that a change is coming to The Project Management Professional

Understanding Threat Actors 101
Understanding Threat Actors 101 It is important to have a strong and robust defense. The success of your defense relies on understanding your enemy. Who is your

Protect, Detect, Respond, and Predict with Certified Network Defender CND
Protect, Detect, Respond, and Predict your Cyber Security landscape with Certified Network Defender CND The only true blue team network defense program! Cybersecurity now dominates the priorities

How to prepare for IT and Cybersecurity Job Interviews
How to prepare for IT and Cybersecurity Job Interviews At our Digital Natives Meetup on October 28th, Prem Jadhwani presented “How to prepare for IT and Cybersecurity

Why you need to learn BIG Data right away!
Big Data Analytics with Splunk and Tableau Big data is a term that describes the large volume of data – both structured and unstructured – that inundates a business on a day-to-day
Building Compelling Resumes for Cybersecurity Jobs
Building Compelling Resumes for Cybersecurity Jobs At our Digital Natives Meetup on Wednesday, October 21st Prem Jadhwani talked about building a compelling resume for cybersecurity jobs. In
MeriTalk Virtual Tech Briefing
MeriTalk Virtual Tech Briefing In case you missed it you are not too late! Prem Jadwani spoke at the MeriTalk Virtual Tech Briefing on October 14th, 2020.

The Three Pillars of AI in Federal Government
The Three Pillars of AI in Federal Government The Big Data Beard Podcast did an interview with GAI President, Jay Lambke, and CTO Prem Jadwhani. Jay and
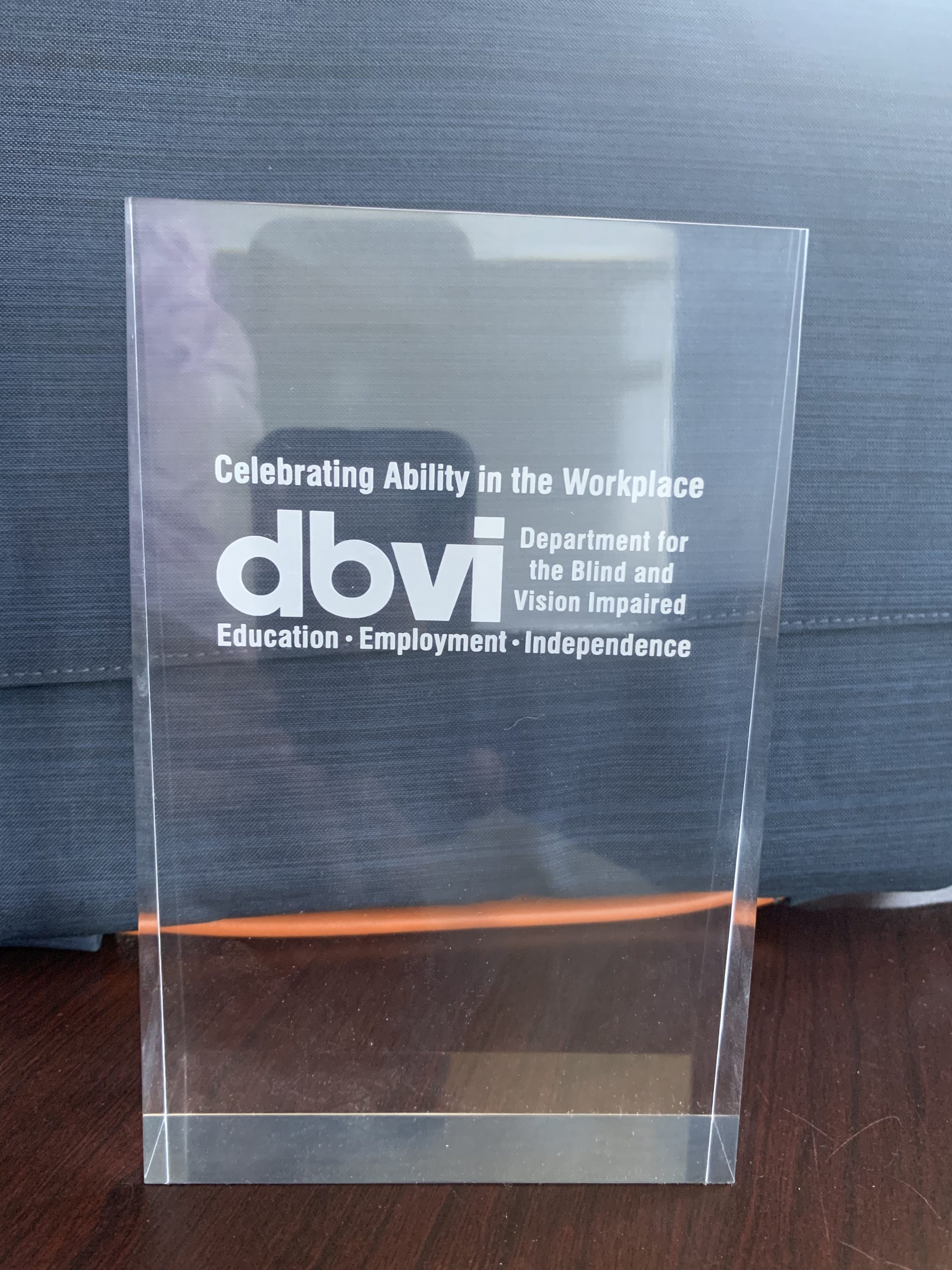
Press Release – Intellectual Point is Awarded DBVI Partner of the Year 2020
Press Release – Intellectual Point is Awarded DBVI Partner of the Year 2020 Sterling, VA (10/7/20) – Intellectual Point announces that it has been awarded DBVI Partner

Check out the CompTIA Security+ SY0-601 Updates
Check out the CompTIA Security+ SY0-601 Updates Every three years CompTIA releases a new and updated version of its exams. This year, on October 4, 2020, CompTIA

CompTIA CySA+ (CS0-002) Update
CompTIA CySA+ (CS0-001) exam will retire October 21, 2020. The new CySA+ (CS0-002) is now available. The CompTIA Cybersecurity Analyst (CySA+) examination is the only intermediate high-stakes

October is National Cybersecurity Awareness Month!
October is National Cybersecurity Awareness Month! This is CISA’s 17th year of National Cybersecurity Awareness Month (NCSAM). In efforts to raise awareness about the importance of cybersecurity
Become an Artificial Intelligence (AI) Expert
Here is the 101 on Becoming an Artificial Intelligence (AI) Expert Artificial Intelligence (AI) is a game changer in amplifying human effectiveness and remove mundane tasks. AI

How to Negotiate your Salary for a Job Offer or Raise!
How to Negotiate your Salary for a Job Offer or Raise! It is always stressful to negotiate your salary offer or ask for a raise. You will

What Cyber Security Career Path are you on?
Careers in cybersecurity We are only a few weeks away from the start of National Cyber Security Awareness Month. It is always good to start with a

Most Powerful Habits of CyberSecurity Professionals
Most Powerful Habits of CyberSecurity Professionals Our ability to improve is largely determined by our habits. Our habits influence the way we respond to any given situation,

Top Cloud Skills Employers Look For
Top Cloud Skills Employers Look For Cloud computing refers to the delivery of computing services over a proprietary network or the Internet. Those services mainly include infrastructure

Why Should I get CompTIA Security+ Certified at Intellectual Point?
Why Should I get CompTIA Security+ Certified at Intellectual Point? CompTIA Security+ is the industry standard for validating baseline skills needed to perform core security functions and

Here is the 101 on the Purple Team
Why a Purple Team? To understand what a purple team is first you need to understand the Red Team and Blue Team. Think of the Red

Top Cyber Security Skills Professionals Recommend Having
Top Cyber Security Skills Professionals Recommend Having Cyber Security is a high demand career with a lot of opportunities. The roles offer competitive pay, growth opportunity, job

Press Release – Intellectual Point to Offer IT Training to U.S. Army Veterans
Intellectual Point to Offer IT Training to U.S. Army Veterans Sterling, VA (8/28/20) – Intellectual Point announces that it has been approved to accept all Army COOL

Certified Chief Information Security Officer (CCISO) program update
Certified Chief Information Security Officer (CCISO) program update EC-Council has major changes to the Certified Chief Information Security Officer (CCISO) program. As many of you know, professionals
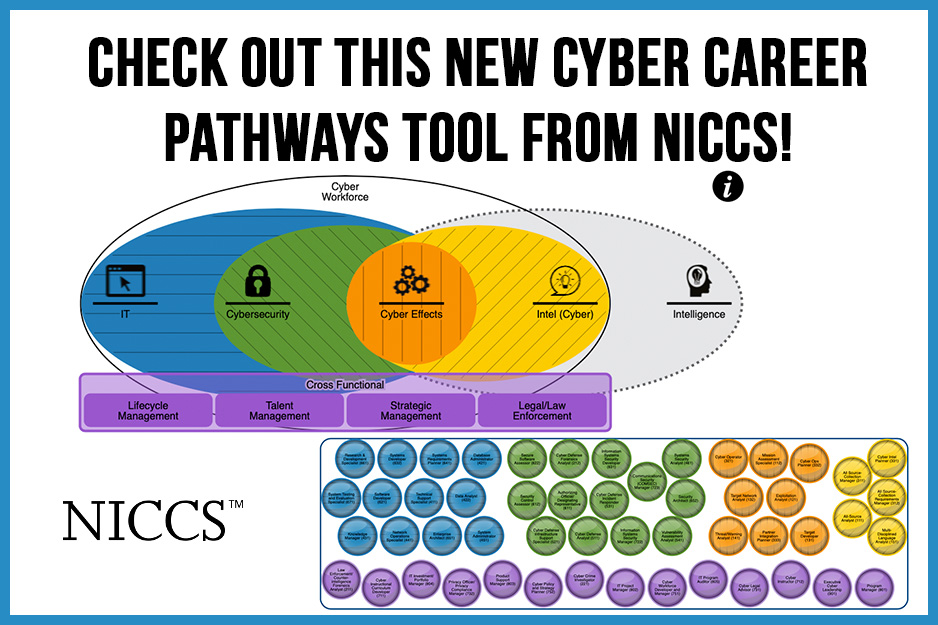
Check Out This New Cyber Career Pathways Tool from NICCS!
Check Out This New Cyber Career Pathways Tool from NICCS! The National Initiative for Cybersecurity Careers and Studies (NICCS) has created a new Cyber Career Pathways

Prem Jadhwani is presenting the “Future of Work” at an IT career opportunities event for youth
Prem Jadhwani is presenting the “Future of Work” at an IT career opportunities event for youth August 13th (Thursday) from 9:30 AM to 10:30 AM Prem

Are you a Project Manager or a Project Leader?
Are you a Project Manager or a Project Leader? The essential skills you need to lead your team. It is hard to find a clear definitions between

Cybersecurity Sneak Peek
Cybersecurity Sneak Peek at Intellectual Point! As you work to adapt to this new world, please know Intellectual Point is here for you. We know you value

Get Ready – PMP Exam Will Change On 2 January 2021
Get Ready – PMP Exam Will Change On 2 January 2021 PMI was set to have the new exam change happen on July 1 2020 but it

AWS Certified Solutions Architect – Associate (SAA-C02)
AWS Certified Solutions Architect – Associate (SAA-C02) The AWS Certified Solutions Architect – Associate certification validates knowledge of how to design and deploy well-architected solutions on AWS

Capture the Flag (CTF) 101
Capture the Flag (CTF) 101 Capture The Flags (CTFs) are a kind of computer security competition. Teams of competitors (or just individuals) are set up against each

Top 10 Most Popular Cybersecurity Certifications In 2020
Top 10 Most Popular Cybersecurity Certifications In 2020 When it comes to selecting the best Cybersecurity Certification is it important to do your research, lucky for you
How to Prepare for the Elastic Certified Analyst Exam
How to Prepare for the Elastic Certified Analyst Exam Have you heard about the new Elastic Certified Analyst Certification? Elastic has created a new certification and you

Are you considering applying to VET TEC? Funding is first come first served.
VET TEC funding is first come first served, so apply today! If you are considering taking advantage of the VET TEC program, be sure to apply as

Why you need to get CISSP Certified to boost your Career!
Why you need to get CISSP Certified to boost your Career! Certified Information Systems Security Professional (CISSP) certification is considered a gold standard of information security competence

10 Tips for writing your best resume
10 Tips for writing your resume Your resume is what gets your foot in the door. Employees use resumes to learn more about applicants and whether they
Join us for CyberWarriors Virtual STEM Workshop!
Join us for Intellectual Point’s CyberWarriors Coding & Automation Experts Virtual STEM Workshop! Class Location: Due to COVID-19 this camp will be Virtual! Age: 13 Years and

We’ve Got Your Back Study Sessions at Intellectual Point
Free Study Sessions with Intellectual Point As we head into another week of social distancing we want to help you get ready for your

CompTIA Cybersecurity Analyst (CySA+) Certification Exam CS0-002
CompTIA Cybersecurity Analyst (CySA+) Certification Exam CS0-002 As attackers have learned to evade traditional signature-based solutions, such as firewalls and anti-virus software, an analytics-based approach within the

CompTIA will be retiring the CompTIA Cloud Essentials+ (CLO-001) exam
CompTIA will be retiring the CompTIA Cloud Essentials+ (CLO-001) exam The new Cloud Essentials+ CLO-002 is currently available to learners exploring the Cloud Essentials+ certification. CompTIA Cloud

PMI & Pearson VUE Now Offer Online Testing Option for PMP® Certification Exam
PMI and Pearson VUE Now Offer Online Testing Option for Project Management Professional (PMP)® Certification Exam Using Pearson VUE’s OnVUE online proctored testing software, PMP candidates can

What are Continuing Education Units (CEUs) and why do you need them?
What are Continuing Education Units (CEUs) and why do you need them? A Continuing Education Unit (CEU), also known as Continuing Education Credit (CEC), is a vital

Get Cisco certified and Cisco DevNet certified today with new online testing
Get Cisco certified and Cisco DevNet certified today with new online testing If you are ready to take a Cisco written exam? If so, you are in

Free Facebook Live Cyber Class with Intellectual Point!
Free Facebook Live Cyber Class with Intellectual Point! Join us for some FREE Cyber Training! Free for anyone who wants to learn more about the topics. Just

Learn at Home, Test at Home: CompTIA Online Testing Information
Learn at Home, Test at Home: CompTIA Online Testing CompTIA is launching online testing with remote proctoring, powered by Pearson OnVUE, allowing candidates to take their CompTIA

Data Science for Managers/Applied Data Science for Cybersecurity VIRTUAL!!!
Data Science for Managers/Applied Data Science for Cybersecurity VIRTUAL!!! BECOME A MASTERMIND WITH THE ABILITY TO IDENTIFY. These interactive courses teach cybersecurity professionals how to use data

Free Red Hat DO101 Training!
Take Introduction to OpenShift Applications for free Red Hat Training is offering its Introduction to OpenShift Applications (DO101) course for free until the end of June. Don’t miss

How To Prepare for the CompTIA Security+ Exam for Certification
How To Prepare for the CompTIA Security+ Exam for Certification This is the most popular technology certification in the world. It is a great foundational training course

You will be able to take CompTIA exams from home starting April 15th
Voucher Extensions, New Online Testing CompTIA will be offering candidates the option of online certification testing starting on April 15, 2020.* Online testing is ideal because candidates
BOGO Deal at Intellectual Point!
Take a Live Online Class – Take a 2nd Class at 50% off! Has social distancing started to get you down? For a limited time only, Intellectual Point

Important PMI Updates
Important PMI Updates We hope you are able to work from home and are staying healthy! There are some important updates from PMI. PMI has announced a

STEM Sessions At Intellectual Point
STEM Sessions at Intellectual Point It has been quite a month, we hope you are hanging in there. These are difficult times and people all over the

AWS Solution Architect SAA-C01 extended until June 30th
AWS Solution Architect SAA-C01 extended until June 30th BREAKING NEWS: SAA-C01 Exam Expiration Extension to June 30, 2020 With the Coronavirus (COVID-19) spreading quickly around the world

URGENT – ONLINE CLASSES
LIVE ONLINE VIRTUAL TRAINING We are closely monitoring the COVID-19 situation. If you are concerned about attending in person or your organization has restricted travel, our Live

Our Intellectual Point Office Is Moving!
Did you hear our office is moving? We have some exciting news! We are moving and we can’t wait for you to see the new office! We

What To Watch For In Cyber Security In 2020
What To Watch For In Cyber Security In 2020 The world has become more interconnected than ever. Thanks to technological advances, computer systems and networks are getting

AWS Certified Solutions Architect Associate Certification Update
AWS Certified Solutions Architect Associate Certification Update The next important update for AWS certification exams is about the happen for one of the most popular certification exams of

Networking Is Essential For Your Career!
Networking Is Essential For Your Career! Networking will help you develop and improve your skillset, stay on top of the latest trends in your industry, keep up-to-date

Why is cloud computing one of the biggest growing career paths?
Why is cloud computing one of the biggest growing career paths? Did you know that the average pay of entry-level Cloud professionals is $124,300? Cloud is a

Influx of IT Jobs in Northern Virginia Means More Scholarships to Pay For Your Education
An influx of IT Jobs in Northern Virginia Means More Scholarships to Pay For Your Education Alexandria and Arlington Residents Get an IT Scholarship Now The growth

Trends That Could Affect Your Next Cybersecurity Role
Trends That Could Affect Your Next Cybersecurity Role CompTIA Released a Report That Highlights the Trends in Cybersecurity Daily Attacks Technology changes and so do cyberattacks. CompTIA
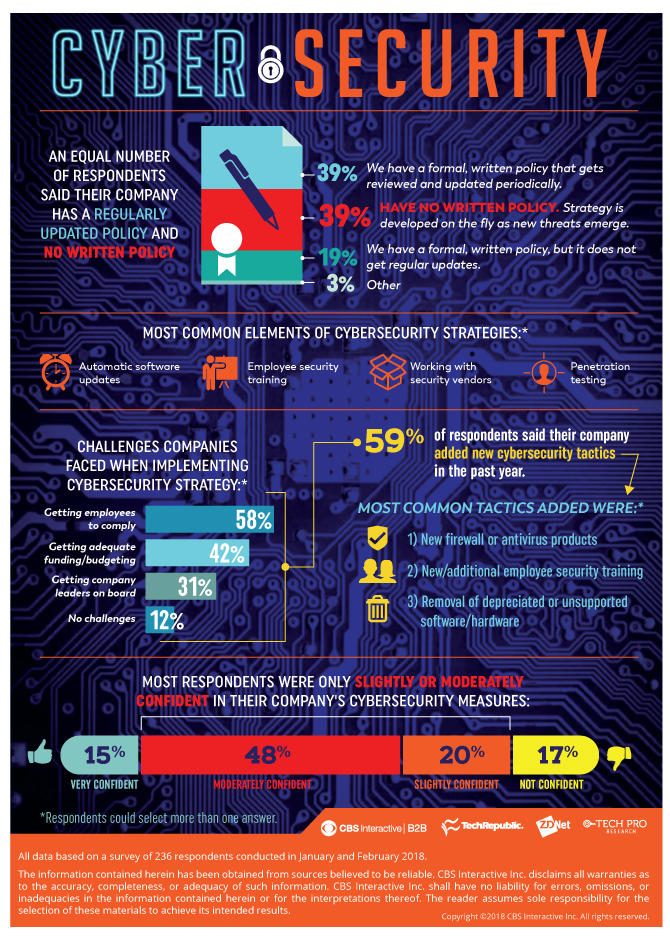
Common Cybersecurity Strategies and Providing IT Solutions in Virginia
Common Cybersecurity Strategies and Providing IT Solutions in Virginia Get a Security Assessment and Evaluation for Your Organization This infographic released by ZDNET shows Cybersecurity strategy: Common
Is Fighting Cyber Attacks Right For You?
Is Fighting Cyber Attacks Right For You? Look at these Attacks and Check If You Can Become a Cyber Warrior These cyberattacks case studies will help you

Prem Jadhwani will be a guest speaker at the ISSA DC Chapter Meeting
Due to COVID-19 This Will Be A Virtual Only Event! Artificial Intelligence & Machine Learning Overview for Decision Makers By Prem Jadhwani Join us on Tuesday,

Average CCSP Salary for 2020 in DC-MD-VA
Average CCSP Salary for 2020 in DC-MD-VA Cloud computing career path is at an all-time high, growing from $266 billion dollar industry during 2020 to a $626

5 of the Best Cloud Certifications to Have on Your Resume
Get an IT Job in a Growing Cloud Computing Market Cloud computing is the delivery of computing services—including servers, storage, databases, networking, software, analytics, and intelligence—over the

IT Sales Training for Small or Large Innovative Companies in DC-MD-VA
Flying Fox is Tapping Into A $84 Billion IT Industry At our Digital Natives Meetup on December 5th of 2019, we had a presentation from Santrum Federal.

CyberWarriors STEM Workshop at Intellectual Point
CyberWarriors STEM Workshop at Intellectual Point For kids 13 years and older, we have a wonderful opportunity to participate in a STEM Workshop in Reston Virginia. Participate

Intellectual Point Awesome Resources!
Are you considering taking a class at Intellectual Point? We have instructors that have real-world experience and teach a learn-by-doing approach. We have flexible schedules that include

Big Changes for CCNP
Big CCNP Changes Are Coming! The CCNP will now be changed from 3-4 exams to only 2. This includes a “core” knowledge exam that everyone has to

Big CCNA changes are coming!
Big CCNA changes are coming! As you have heard, there are big changes coming for Cisco Certifications. On February 24, 2020, Cisco will release a new, consolidated

Are You Ready to Launch Your Career In Cloud Computing?
Are You Ready to Launch Your Career In Cloud Computing? In our last Digital Natives Meetup, Prem Jadhwani talked about how to break into a Cloud Computing

Certified Authorization Professional CAP/RMF should be your next certification!
Does your current job role focus in and around authorizing and maintaining information systems? If so, we have the answer to advance your career! Earn your Certified

ITIL® 4 vs ITIL® V3: What’s New?
ITIL® 4 vs ITIL® V3: What’s New? Axelos is releasing a new version of the Information Technology Infrastructure Library (ITIL®). ITIL® 4 vs ITIL® V3: What’s New?

Are you trying to start a cyber security career?
Are you trying to start a cybersecurity career? In case you missed it we had a very successful #DigitalNatives meetup on September 17th. We had a great
CompTIA Linux+ XK0-004
On October 1st, 2019 CompTIA will be retiring the Linux+ LX0-103 and LX0-104 exam. Are you ready for CompTIA Linux+ XK0-004? If you are in the process
AI & Machine Learning Jobs are In High Demand
AI & Machine Learning Jobs are In High Demand When you look around these days you see AI everywhere! It is a hot field where AI &

(ISC)² Refreshes its Certified Cloud Security Certification (CCSP) Exam
Certified Cloud Security Professional (CCSP) Certification Exam Changes Effective August 1, 2019, the first update that has been made to the Certified Cloud Security Certification (CCSP) exam

Why Choose Intellectual Point For Your Training to Pass Your Certification Exam?
Why Choose Intellectual Point For Your Training? We know that certification exam can seem overwhelming and scary. Intellectual Point takes the stress and worries out of the
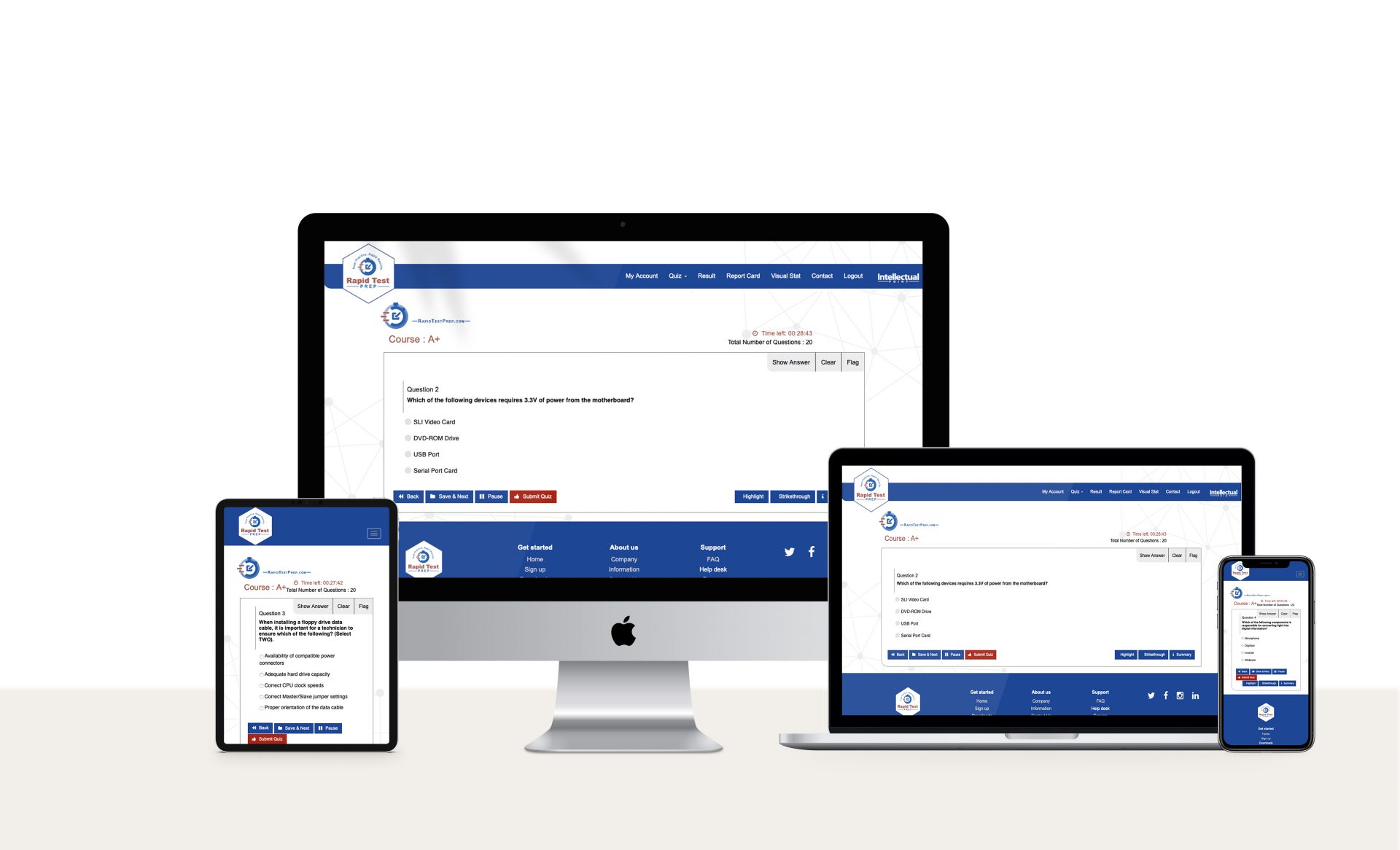
Rapid Test Prep Is Your Tool For Success
Study with Rapid Test Prep Powered by Intellectual Point The best way for success in passing your test is to practice. Once you take a class with

PMI® Announcement About PMP® Exam!
PMI® Announced That The PMP® Exam Will Change On December 16, 2019 The Project Management Institute (PMI)® announced that a change is coming to The Project Management
CompTIA CySA+ and CompTIA Cybersecurity
Are you looking to take your cybersecurity career to the next level but you aren’t sure where to turn next? Maybe you have taken all the entry-level
Certified Ethical Hackers: Stopping cybercrime in its tracks
Certified Ethical Hackers: Stopping cybercrime in its tracks Cyberattacks are all too common in today’s world and they do not come without consequences. In recent years, millions

Intellectual Point Testing Center Guidelines
Intellectual Point is an authorized Pearson VUE, Kryterion, ISO, PAN & DSST, CLEP, EC-Council as well as Castle Testing Center. We are located in Northern Virginia near

We’re here to help you every step of the way!
We want to help you achieve your goals. From acquiring and validating essential IT skills to leveraging and improving your credentials, we’re here to help. View our

Cisco Introduces New Cloud and IoT Certifications to Address Key IoE Skills
Cisco announced new IoT and Cloud-focused career certifications. The Internet of Everything (IoE) has caused rapid technology shifts. The IoE brings together people, process, data, and things

New Cisco Certification Levels Updates 2019
New Cisco Certification Updates 2019 Have you heard the big news from the Cisco Live in San Diego? Cisco announced a major revamp to their entire certification
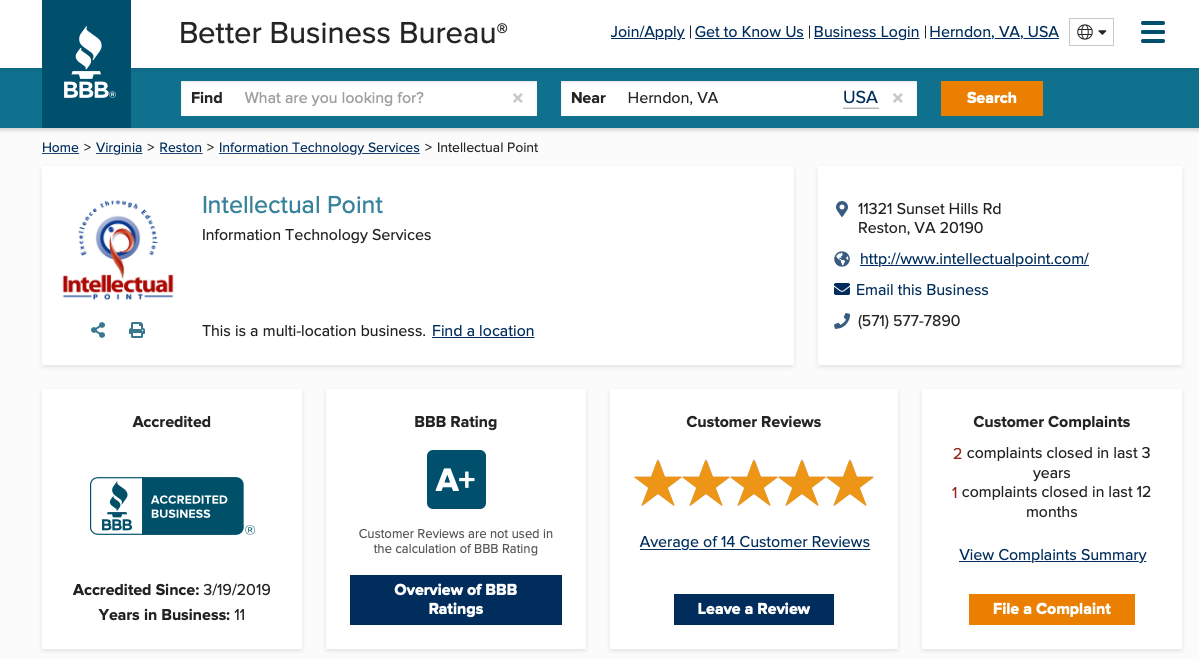
Intellectual Point Commits to the BBB Standards of Trust
Intellectual Point Commits to the BBB Standards of Trust This week, Intellectual Point announced its recent accreditation by the BBB serving Metro Washington DC and Eastern PA.
Is Artificial Intelligence the same as Machine Learning?
Understanding the difference between AI and ML.
Choosing the Right Certification
How to maximize your training time and dollars for long term success.
Free Newsletter
How to Pass the CompTIA Security+ Exam at the First Attempt
How to pass the CompTIA Security+ Exam at the First Attempt First, you need to familiarize yourself with what is on the test. Get to know
What is your Cyber Security Career Path?
What is your Cyber Security Career Path? At Intellectual Point, we are here to help you find the best career path for your future. There are many

How to Identify and Mitigate the Impact of the Sunburst Hack
How to Identify and Mitigate the Impact of the Sunburst Hack Sunburst Attack Overview On December 13th, 2020 the world became publicly aware of a sophisticated and
Hello, this is a friendly reminder about the PMP® Exam that will change on January 2, 2021!
Hello, this is a friendly reminder about the PMP® Exam that will change on January 2, 2021! The Project Management Institute (PMI)® announced that a change is coming to

Hello, Check out these Cybersecurity Career Tips and Tricks! ?
Hello, Check out these Cybersecurity Career Tips and Tricks! ? Intellectual Point is proud to support you with your career no matter what stage you are in.
Free Study Sessions, BOGO deals, and much more!
Free Study Sessions, BOGO deals, and much more! How to Prepare for the CompTIA Security+ Exam This is the most popular technology certification in the world. It
Stay Safe & Keep Learning with Intellectual Point! ?
Stay Safe & Keep Learning with Intellectual Point! ? During this time of encouraging social distancing, IP is doing what it can to help individuals and the IT
You won’t see this deal again until 2024! ?
You won’t see this deal again until 2024! ? Seven hackers have now made a million dollars each from bug bounties, says HackerOne. Ethical Hacking is becoming

Is Your Head Stuck In the Clouds Today! ?
Is Your Head Stuck In the Clouds Today! ? You don’t have to be in love with your head stuck in the clouds to learn how important

2020 is here…Are You Ready? Come Learn More at Intellectual Point ?
2020 is here…Are You Ready? ? Cybercriminals are evolving their tactics as the security industry tries to keep up to be protected. It is a constantly changing

ITIL 4® is here are you ready? Come Learn More at Intellectual Point ?
ITIL 4® is here are you ready? Come Learn More at Intellectual Point ? ITIL ® is the world’s leading best practice framework for managing IT services.

National Cybersecurity Awareness Month ?
National Cybersecurity Awareness Month ? Held every October, National Cybersecurity Awareness Month (NCSAM) is a collaborative effort between government and industry to raise awareness about the importance

Memorial Day Savings and MORE!
Staying Cyber Safe During Memorial Day As Memorial Day approaches, the Cybersecurity and Infrastructure Security Agency (CISA) reminds users to stay cyber safe. Users should be cautious

Testing Center Tips at Intellectual Point!
Testing Center Tips at Intellectual Point! Be sure to watch our Study Tip videos for helpful information. We are proud to help you get ready for the
Major benefits of getting an AWS certification
Major benefits of getting an AWS certification In general, earning a hands-on IT certification can provide some huge advantages. If you’re on the fence about getting your
Calling ALL Cybersecurity Talent!
Calling ALL Cybersecurity Talent! Why the Cybersecurity Talent Shortage Is The Greatest Threat Businesses Face Today With the economy booming in the tech sector and unemployment rates
What is domain hijacking?
US Gov issues emergency directive after wave of domain hijacking attacks The US Department of Homeland Security (DHS) has issued an emergency directive tightening DNS security after
To succeed in your career, you need to be a hacker!
To succeed in your career, you need to be a hacker! Intellectual Point Wishes You A Very Happy Holiday! At #IntellectualPoint , we are happy to be
Spring updates that can help you grow your career ?
Spring updates that can help you grow your career ? INTELLECTUAL POINT SPRING UPDATES As Spring rolls in, so do our available certification options. We are proud
How can Intellectual Point help with your New Year’s resolutions?
How can Intellectual Point help with your New Year’s resolutions? We at Intellectual Point want to wish you a very Happy New Year! This is the time
Ready to make between $150,000 and $175,000 annually?
Ready to make between $150,000 and $175,000 annually? Salaries for Blockchain engineers are skyrocketing, now on par with AI experts Blockchain engineers are making between $150,000 and
Get your CISSP and then use one of the Top 6 Linux Operating Systems for Privacy
The 6 Best Linux Operating Systems For Privacy Out of all modern operating system platforms, Linux is considered one of the best when it comes to privacy.
happy clients
What Our Customers Say - Based on over 600+ Reviews!






























